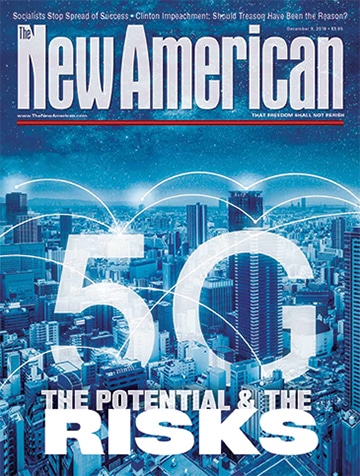
Security and Surveillance in a 5G World
The rollout of 5G mobile communications as an upgrade to existing 4G networks promises to deliver a new era in data throughput and bandwidth, enabling new capabilities that will improve economic production, drive job growth, increase prosperity, and enable new, immersive entertainment possibilities. And that’s just a few of the many benefits that may be derived from 5G. But just like any technology, 5G can drive negative outcomes in addition to positive ones.
One of the best pro-freedom writers working today recently fielded a question about 5G from one of his readers. Eric Peters reviews cars from a staunchly pro-freedom viewpoint, and he often has useful perspective to share with his readers. Asked what he thought about the dangers of 5G, he replied that his chief concern was its potential impact on our freedoms.
“We’re told 5G is harmless — in terms of health — and maybe so,” he wrote. “But will it be harmless in terms of our liberty? Our privacy? Our right to be free from ubiquitous monitoring — and control? I have grave doubts about that.”
JBS Member?
Sign in with your ShopJBS.org account.
 Subscribe Now
Subscribe Now
- 12 Issues Per Year
- Digital Edition Access
- Digital Insider Report
- Exclusive Subscriber Content
- Audio provided for all articles
- Unlimited access to past issues
- Cancel anytime.
- Renews automatically
 Subscribe Now
Subscribe Now
- 12 Issues Per Year
- Print edition delivery (USA)
*Available Outside USA - Digital Edition Access
- Digital Insider Report
- Exclusive Subscriber Content
- Audio provided for all articles
- Unlimited access to past issues
- Cancel anytime.
- Renews automatically